They got a warrant by noting that the IP address of the activist was tied to child porn, but they did not tell the judge that the activist was running a Tor node, which meant that he was not the origin point, and had no way to know the content of the material:
One week after Seattle police searched the home of two well-known privacy activists for child porn and found nothing, critics are questioning why the department failed to include a key piece of information in its application for a warrant—the fact that the activists operated a Tor node out of their apartment, in order to help internet users all over the world surf the web anonymously.Of course, there will be on consequences for the police who deceived the judge.
"You knew about the Tor node," said Eric Rachner, a cybersecurity counsultant and co-founder of Seattle's Center for Open Policing, addressing the police department on Twitter, "but didn't mention it in warrant application. Y'all pulled a fast one on the judge... you knew the uploader could have been literally anyone in the world."
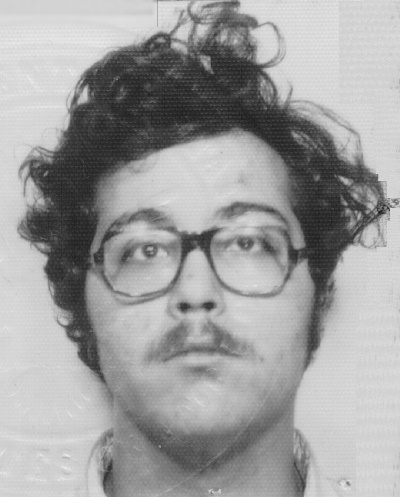
At 6 a.m. on March 30, Seattle police showed up at the Queen Anne apartment of Jan Bultmann and David Robinson with a search warrant to look for child porn, based on a tip that traced an illicit video to their IP address. Six officers arrived with two vans and spent over an hour doing forensic searches on the computers in the home. One officer stood in the bedroom and watched as Robinson got dressed.
They didn't find anything. Bultmann and Robinson, both board members of the Seattle Privacy Coalition, were released after being detained in a van, but they were left shaken and upset.
………
Bultmann and Robinson had publicly advertised that they operated a Tor exit relay node—a node in the global Tor network, whose purpose is to give users the ability to browse the web anonymously. They said they operated the node as a service to dissidents in repressive countries, knowing full well that criminals might use it as well, much like any other communication tool. Tor stands for "the onion router," a mechanism by which information is encrypted in layers as it passes through multiple, randomized nodes in the network.
In the aftermath of the search, the question was whether Seattle police had done their technical due diligence: Did they recognize that Bultmann and David were operating a Tor node? If so, did they realize that a tip about child porn coming from that IP address, absent any other evidence, likely meant someone else in another part of the world had uploaded the material and it had been randomly routed through their node?
………
"It's like raiding the mailman's house for delivering an illegal letter with no return address," said one commenter on the tech website YCombinator. "Sure, it could have been sent by the mailman, but it could have been sent by anyone. There isn't any more reason to suspect the exit node operators than anyone else in the whole world who could also have used the exit node."
The warrant application (PDF), signed by King County Superior Court Judge Bill Bowman, makes no mention of the Tor node, much less Bultmann and Robinson's public roles as privacy activists. Nor does a warrant application dated February 24 to obtain subscriber records related to the address from Wave G, the Internet service provider. Both documents suggest that Bultmann and Robinson are ordinary web users with a private home connection.
………
SPD spokesperson Sean Whitcomb said the department understands how Tor works and that before executing the search, officers knew that Bultmann and Robinson operated the Tor node out of their apartment. "Knowing that, moving in, it doesn't automatically preclude the idea that the people running Tor are not also involved in child porn," Whitcomb told NPR. "It does offer a plausible alibi, but it's still something that we need to check out."
But in a statement today, the department said its detectives didn't know about the Tor node when they filed the warrant application on March 28. If true, this means detectives took notice of the Tor node after the judge approved the warrant, then carried out the exhaustive early-morning search two days later anyway.
Robinson questions whether police deliberately delayed checking the IP address against the public list of Tor nodes in order to avoid sharing exculpatory information with the judge. He believes a sound investigation would have checked the IP address as soon as the tip came in. "Why spoil a perfectly good warrant with facts?" he asked.
There never is.

0 comments :
Post a Comment